
Different meaning IDS: Intrusion Detection System A visual metaphor: If the firewall is the door lock of a building, then IDS is the monitoring system in this building. Once the thief climbs the window into the building, or the insiders cross the line, the real-time monitoring system will detect the situation and issue a warning.
Intrusion detection system (abbreviated as "IDS") is a network security device that monitors network transmission in real time, sends alarms or takes proactive response measures when suspicious transmission is found.The difference between it and other network security devices is that IDS is a proactive security protection technology.
Principle: Intrusion detection system (IDS) can be defined as a system that identifies and deals with the malicious use of computers and network resources accordingly.
A complete intrusion detection system IDS must be a distributed system based on both host and network-based. In addition, the number of intrusion methods that can be identified and whether the latest intrusion methods are updated in time are also key indicators for evaluating the intrusion detection system.
Analysis: IDS is the abbreviation of "Intrusion Detection Systems" in English, which means "intrusion detection system" in Chinese.
Record logs: The monitoring system usually has detailed logs, including login time, IP address and other information. These logs can be viewed by administrators or system maintainers. If an unauthorized login record is found, it will cause suspicion.
The solution to this situation is relatively simple. As long as the whole system is powered by purification power or online UPS, it can be basically solved. There is a strong source of interference near the system. This can be judged through investigation and understanding.
Once someone is ready to break into the surveillance or do something in front of the door, it will be detected by their own control center.

intrusion detection system (intrusion detection system, abbreviated as "IDS") is a network security device that monitors network transmission in real time and issues alerts or takes proactive response measures when suspicious transmissions are found. The difference between it and other network security devices is that IDS is a proactive security protection technology.
The back door is a small hole in the computer security system that allows users to bypass normal security measures to enter the system.
General Web deception uses two technical means, namely URL address rewriting technology and related credit information masking technology. Use URL addresses to make these addresses point to the attacker's web server, that is, the attacker can add his own web address in front of all URL addresses.
Worms are harmful program events in information security events. Worms are a kind of self-replicable code and spread through the network, usually without human intervention. After the worm invades and completely controls a computer, it will use the machine as a host, and then scan and infect other computers.
If the CMOS is destroyed, you can discharge the CMOS and then reset it to solve the problem.
What's more, after the virus attack, it is likely that you will not be able to enter the system, so backing up important files in time after poisoning is one of the most important ways to reduce losses. Comprehensive anti-virus. When there is no need to worry, the virus can be investigated and killed.
First of all, if you find that your computer has been hacked, you should immediately disconnect from the Internet to prevent hackers from continuing to attack. Secondly, you can choose to use the software to detect and remove viruses. If the software can't handle it, you can restore the computer to the factory settings.
How to manage cross-border complexity-APP, download it now, new users will receive a novice gift pack.
Different meaning IDS: Intrusion Detection System A visual metaphor: If the firewall is the door lock of a building, then IDS is the monitoring system in this building. Once the thief climbs the window into the building, or the insiders cross the line, the real-time monitoring system will detect the situation and issue a warning.
Intrusion detection system (abbreviated as "IDS") is a network security device that monitors network transmission in real time, sends alarms or takes proactive response measures when suspicious transmission is found.The difference between it and other network security devices is that IDS is a proactive security protection technology.
Principle: Intrusion detection system (IDS) can be defined as a system that identifies and deals with the malicious use of computers and network resources accordingly.
A complete intrusion detection system IDS must be a distributed system based on both host and network-based. In addition, the number of intrusion methods that can be identified and whether the latest intrusion methods are updated in time are also key indicators for evaluating the intrusion detection system.
Analysis: IDS is the abbreviation of "Intrusion Detection Systems" in English, which means "intrusion detection system" in Chinese.
Record logs: The monitoring system usually has detailed logs, including login time, IP address and other information. These logs can be viewed by administrators or system maintainers. If an unauthorized login record is found, it will cause suspicion.
The solution to this situation is relatively simple. As long as the whole system is powered by purification power or online UPS, it can be basically solved. There is a strong source of interference near the system. This can be judged through investigation and understanding.
Once someone is ready to break into the surveillance or do something in front of the door, it will be detected by their own control center.

intrusion detection system (intrusion detection system, abbreviated as "IDS") is a network security device that monitors network transmission in real time and issues alerts or takes proactive response measures when suspicious transmissions are found. The difference between it and other network security devices is that IDS is a proactive security protection technology.
The back door is a small hole in the computer security system that allows users to bypass normal security measures to enter the system.
General Web deception uses two technical means, namely URL address rewriting technology and related credit information masking technology. Use URL addresses to make these addresses point to the attacker's web server, that is, the attacker can add his own web address in front of all URL addresses.
Worms are harmful program events in information security events. Worms are a kind of self-replicable code and spread through the network, usually without human intervention. After the worm invades and completely controls a computer, it will use the machine as a host, and then scan and infect other computers.
If the CMOS is destroyed, you can discharge the CMOS and then reset it to solve the problem.
What's more, after the virus attack, it is likely that you will not be able to enter the system, so backing up important files in time after poisoning is one of the most important ways to reduce losses. Comprehensive anti-virus. When there is no need to worry, the virus can be investigated and killed.
First of all, if you find that your computer has been hacked, you should immediately disconnect from the Internet to prevent hackers from continuing to attack. Secondly, you can choose to use the software to detect and remove viruses. If the software can't handle it, you can restore the computer to the factory settings.
HS code alignment with import licensing
author: 2024-12-24 00:13HS code consulting for exporters
author: 2024-12-24 00:12Country-specific HS code exemptions
author: 2024-12-23 23:46How to identify emerging market suppliers
author: 2024-12-23 23:22Predictive models for trade demand
author: 2024-12-23 23:18Global trade supply chain modeling
author: 2024-12-23 23:56Minimizing duties via HS code optimization
author: 2024-12-23 23:19Cleaning agents HS code classification
author: 2024-12-23 22:30Trade data for risk scoring models
author: 2024-12-23 22:29 How to leverage analytics in procurement
How to leverage analytics in procurement
393.61MB
Check Global trade data integration services
Global trade data integration services
978.26MB
Check HS code-based forecasting for raw materials
HS code-based forecasting for raw materials
254.46MB
Check How to reduce documentation errors
How to reduce documentation errors
182.18MB
Check Marble and granite HS code references
Marble and granite HS code references
831.57MB
Check HS code-driven export incentives
HS code-driven export incentives
157.29MB
Check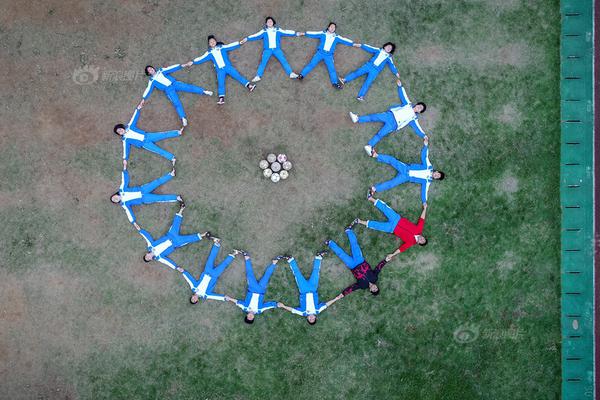 Predictive trade data cleaning
Predictive trade data cleaning
527.14MB
Check Global cross-border payment tracking
Global cross-border payment tracking
274.93MB
Check HS code utilization in digital trade documents
HS code utilization in digital trade documents
136.74MB
Check Global trade data for currency hedging
Global trade data for currency hedging
131.72MB
Check Real-time delivery time predictions
Real-time delivery time predictions
592.98MB
Check HS code correlation with global standards
HS code correlation with global standards
992.51MB
Check HS code-based cost modeling for imports
HS code-based cost modeling for imports
428.94MB
Check Machine tools HS code classification
Machine tools HS code classification
123.96MB
Check How to interpret global trade indices
How to interpret global trade indices
243.27MB
Check Predictive supplier scoring algorithms
Predictive supplier scoring algorithms
161.21MB
Check Top global trade data insights
Top global trade data insights
221.62MB
Check trade data analysis
trade data analysis
974.52MB
Check Supplier compliance audit automation
Supplier compliance audit automation
563.65MB
Check How to leverage big data in trade
How to leverage big data in trade
277.89MB
Check Trade data for consumer electronics
Trade data for consumer electronics
542.61MB
Check Pharma active ingredients HS code checks
Pharma active ingredients HS code checks
684.94MB
Check HS code-driven trade finance optimization
HS code-driven trade finance optimization
193.76MB
Check Global trade lead generation tools
Global trade lead generation tools
943.82MB
Check HS code-based inventory forecasting
HS code-based inventory forecasting
438.67MB
Check Mining equipment HS code references
Mining equipment HS code references
564.32MB
Check Global trade compliance dashboards
Global trade compliance dashboards
699.73MB
Check Global trade fair insights
Global trade fair insights
798.25MB
Check HS code compliance training modules
HS code compliance training modules
351.89MB
Check Apparel HS code mapping for global exports
Apparel HS code mapping for global exports
282.71MB
Check Industrial gases HS code verification
Industrial gases HS code verification
526.68MB
Check Rare earth minerals HS code classification
Rare earth minerals HS code classification
897.26MB
Check Medical implants HS code classification
Medical implants HS code classification
229.78MB
Check Pharma supply chain mapping by HS code
Pharma supply chain mapping by HS code
992.43MB
Check Dynamic duty drawback calculations
Dynamic duty drawback calculations
611.25MB
Check Industrial lubricants HS code classification
Industrial lubricants HS code classification
191.48MB
Check
Scan to install
How to manage cross-border complexity to discover more
Netizen comments More
613 Construction materials HS code references
2024-12-24 00:03 recommend
1642 Customizable trade data dashboards
2024-12-23 23:37 recommend
1403 Granular HS code detail for compliance officers
2024-12-23 23:14 recommend
609 Germany international trade insights
2024-12-23 23:09 recommend
1742 HS code automotive parts mapping
2024-12-23 22:25 recommend