
Real-time import quota alerts-APP, download it now, new users will receive a novice gift pack.
HS code correlation with export refunds
author: 2024-12-24 02:00Comprehensive customs ruling database
author: 2024-12-24 01:52Cocoa and chocolate HS code insights
author: 2024-12-24 01:31Export data analysis for consumer goods
author: 2024-12-24 01:22HS code alignment for halal imports
author: 2024-12-24 00:43GCC HS code-based tariff systems
author: 2024-12-24 02:41Medical consumables HS code data
author: 2024-12-24 02:38Fisheries products HS code classification
author: 2024-12-24 01:52How to leverage big data in trade
author: 2024-12-24 01:19How to integrate HS codes in ERP
author: 2024-12-24 00:29 Deriving product origin via HS code
Deriving product origin via HS code
685.18MB
Check HS code lookup for global trade
HS code lookup for global trade
583.29MB
Check Agriculture import export insights
Agriculture import export insights
489.74MB
Check Supply chain sustainability metrics
Supply chain sustainability metrics
288.29MB
Check Global trade analytics for decision-makers
Global trade analytics for decision-makers
852.73MB
Check Supply chain data
Supply chain data
693.31MB
Check How to optimize shipping schedules
How to optimize shipping schedules
487.13MB
Check Renewable energy equipment HS code mapping
Renewable energy equipment HS code mapping
474.48MB
Check Minimizing duties via HS code optimization
Minimizing duties via HS code optimization
926.14MB
Check HS code-based customs valuation tools
HS code-based customs valuation tools
258.21MB
Check HS code indexing for procurement catalogs
HS code indexing for procurement catalogs
622.35MB
Check Supply chain sustainability metrics
Supply chain sustainability metrics
332.38MB
Check Global trade data integration services
Global trade data integration services
449.44MB
Check Advanced commodity classification analytics
Advanced commodity classification analytics
271.67MB
Check China HS code interpretation guide
China HS code interpretation guide
157.55MB
Check Precision machining HS code checks
Precision machining HS code checks
491.58MB
Check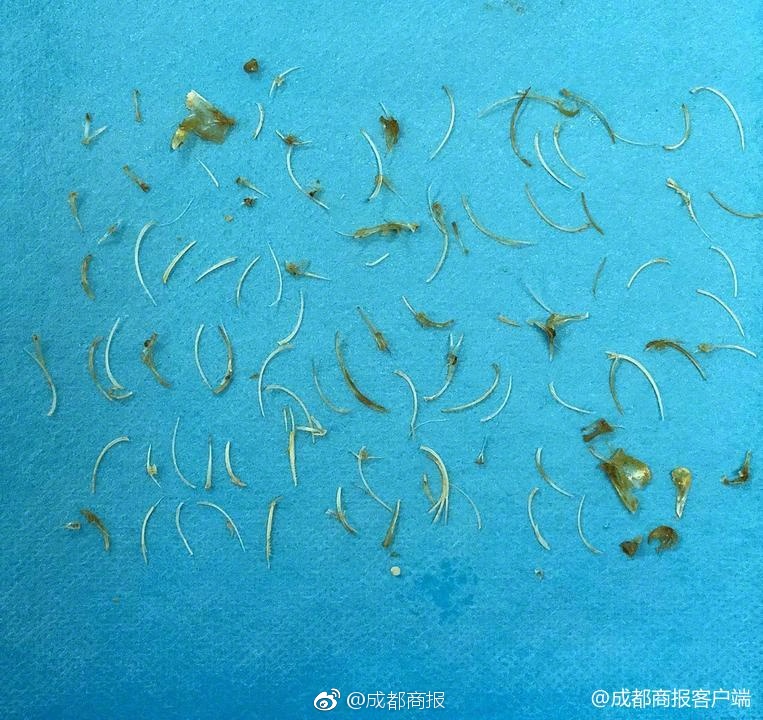 Trade intelligence for emerging markets
Trade intelligence for emerging markets
198.23MB
Check HS code compliance for Pacific Island nations
HS code compliance for Pacific Island nations
486.98MB
Check HS code-based duty drawback claims
HS code-based duty drawback claims
543.89MB
Check Latin America trade data insights
Latin America trade data insights
988.52MB
Check HS code-driven logistics partner selection
HS code-driven logistics partner selection
695.45MB
Check HS code-based supply risk mitigation
HS code-based supply risk mitigation
548.22MB
Check Cocoa and chocolate HS code insights
Cocoa and chocolate HS code insights
224.83MB
Check Customized market entry reports
Customized market entry reports
227.82MB
Check How to find reliable global suppliers
How to find reliable global suppliers
781.53MB
Check Country block exemptions by HS code
Country block exemptions by HS code
669.24MB
Check Top trade data plugins for analytics
Top trade data plugins for analytics
738.93MB
Check shipment records analysis
shipment records analysis
361.41MB
Check HS code-based trade data analytics
HS code-based trade data analytics
194.44MB
Check Shipment data platform
Shipment data platform
719.22MB
Check Global trade tender evaluation tools
Global trade tender evaluation tools
672.88MB
Check Global trade intelligence for banking
Global trade intelligence for banking
281.82MB
Check How to identify emerging supply hubsHolistic trade environment mapping
How to identify emerging supply hubsHolistic trade environment mapping
391.44MB
Check Australia import export data visualization
Australia import export data visualization
141.38MB
Check Detailed trade data mapping tools
Detailed trade data mapping tools
982.73MB
Check global trade intelligence
global trade intelligence
157.61MB
Check
Scan to install
Real-time import quota alerts to discover more
Netizen comments More
130 HS code guides for automotive parts
2024-12-24 02:29 recommend
204 Trade intelligence for emerging markets
2024-12-24 01:40 recommend
856 Asia trade analytics platform
2024-12-24 01:34 recommend
1306 Organic textiles HS code verification
2024-12-24 00:34 recommend
2830 Import export compliance audits
2024-12-24 00:32 recommend